The global rise of cryptocurrency represents a major transformation of how people store and transfer value. Cryptocurrencies took less than 10 years to become popular, compared to hundreds of years for paper money. Currently, less than 10% of money exists in physical form. The majority of money is simply a digital balance in a bank.
The concept of money is undergoing change for the first time in hundreds of years. The Internet freed information to the global population; and likewise cryptocurrencies will give people more direct control over their finances. Read our whitepaper summary to find out more.
Tech & Architecture
Payment Coin has been derived from the Bitcoin source code. On a technical level, baseline Payment Coin is nearly identical to Bitcoin, meaning that pretty much all software upgrades created for Bitcoin can be equally well implemented into Payment Coin.
The initial differences between the two relate mainly to block generation times, coin issuance and the mining algorithm. Payment Coin block generation times are targeted at 2.5 minutes instead of the 10-minute block generation target used by Bitcoin. The idea behind the modification is to allow for 4x faster confirmation times than Bitcoin.
Even though the block generation target is 4x that of Bitcoin, the block reward remains the same, starting at POD 50 per block. However, Payment Coin block rewards are cut in half every 840,000 blocks, as opposed to every 210,000 blocks in Bitcoin. As a result, the Payment Coin inflation schedule plays out over the same length as Bitcoin (~130 years), but the total number of Payment Coins will be 4x that of Bitcoin: a total of POD ~84MM.
The Scrypt mining algorithm has been selected intentionally to be incompatible with existing Bitcoin mining hardware, thereby ensuring a state of non-competitiveness between the two coins in terms of operational hash power. This will be upgraded to a Parallax variant in 2022.
The benefits of this architectural set-up is that Payment Coin can easily incorporate any Bitcoin developments and bug fixes whilst adding innovative new features and functionality in parallel. This is an often overlooked when looking at altcoin foundations.
Coin Specifications
- Fair launch: mainnet live 14 Feb 2018
- Block reward: 50 POD
- Block halving: 840,000 blocks
- Block Time: ~2.5 Minutes
- Difficulty Adjustment Interval: Every 2016 blocks
- Maximum supply: 84,000,000 POD
- Hashing Algorithm: Scrypt (upgrade to Parallax variant 2022)
- Distribution: Available to public on launch: 99.5%
- Distribution: Pre-mine: 0.5% (saved for good causes and inspired Pineapple Fund)
- Ticker Symbol: POD
- RPC Ports: 2332/2333
Target Emission ScheduleTarget Emission ScheduleYear Mining Reward
2018 50.000
2022 25.000
2026 12.500
2030 6.250
2034 3.125
2038 1.563
2042 0.781
2046 0.391
2050 0.195
2054 0.098
2058 0.049
2062 0.024
2066 0.012
2070 0.006
2074 0.003
2078 0.002
2082 0.001
Payment Coin (POD) Whitepaper
Electronic Cash Without Intermediaries
Parallax 2016 (Satoshi Nakamoto 2008)
Abstract
“Payment Coin is a programmable P2P social currency and distributed economy. First we aim to built basic P2P currency and once established, dynamic smart money is an easy next step.” – Parallax.
The Problem: There is no way of making peer-to-peer payments online that bypass financial institutions. Some solutions exist that utilise digital signatures, but these require a intermediary or third party to ensure that the digital value is not spent more than once (double spending)
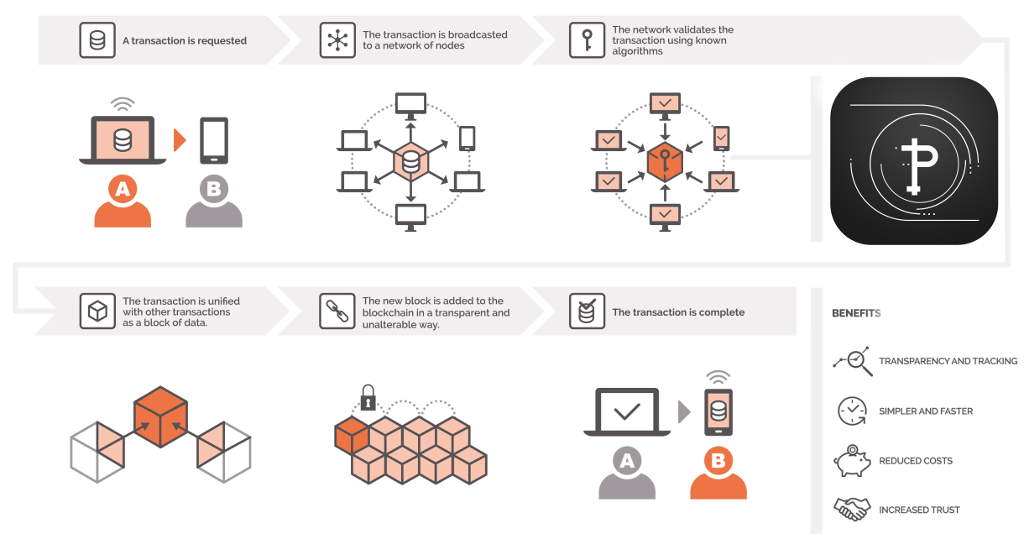
The Solution: A pure peer-to-peer network that hashes transactions, using cryptography, into a chain of hash-based proof-of-work records. The chain provides proof of the chronological sequence of transactions and the verification from “honest” nodes that collectively control the largest pool of CPU power.
1. Introduction
Commerce on the Internet has come to rely almost exclusively on financial institutions serving as intermediaries to process electronic payments. While the system works well enough for most transactions, it still suffers from the inherent weaknesses of the intermediary based model.
Existing models suffer from:
- Reliance on financial institutions
- The need for centralized parties to process payments
- Non-reversible transactions which in turn increase transaction costs and further accentuate the need for intermediaries and centralised third parties
- An acceptance that some fraud is inevitable.
These costs and payment uncertainties can be avoided in person by using physical currency, but no mechanism exists to make payments over a communications channel without an intermediary.
What is needed is an electronic payment system based on cryptographic proof instead of intermediaries, allowing any two willing parties to transact directly with each other without the need for a third party.
New model benefits from:
- Cryptographic proof rather than intermediaries
- Enables parties to transaction directly with one another bypassing any centralized third party
- Protects individuals from fraud
2. Transactions
We define an electronic coin as a chain of digital signatures. Each owner transfers the coin to the next by digitally signing a hash of the previous transaction and the public key of the next owner and adding these to the end of the coin. A payee can verify the signatures to verify the chain of ownership.
The problem of course is the payee can’t verify that one of the owners did not double-spend the coin. A common solution is to introduce a intermediary central authority, or mint, that checks every transaction for double spending. After each transaction, the coin must be returned to the mint to issue a new coin, and only coins issued directly from the mint are trusted not to be double-spent. The problem with this solution is that the fate of the entire money system depends on the company running the mint, with every transaction having to go through them, just like a bank.
We need a way for the payee to know that the previous owners did not sign any earlier transactions. The only way to confirm the absence of a transaction is to be aware of all transactions.
To accomplish this without a centralized party, transactions must be publicly announced[1]:
- Every owner of an electronic coin passes it to the next owner by digitally signing:
- A hash of the previous transaction
- The public key of the new owner
- Adding the above 2 components to the end of the electronic coin
- The new owner is in turn able to verify the signatures which in turn allows him/her to verify the ownership of the electronic coin
- In order to achieve the above without a centralized third party requires that the transactions are:
- Declared publicly
- Confirmed through a system whereby all participants (nodes) agree the history and order in which the transaction was received
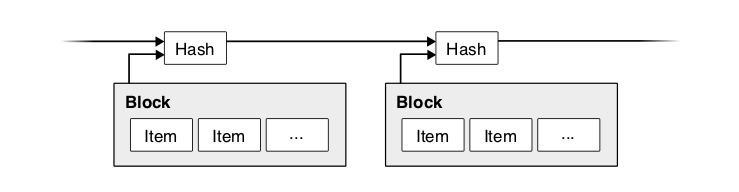
3. Timestamp Server
The solution we propose begins with a timestamp server. A timestamp server works by taking a hash of a block of items to be timestamped and widely publishing the hash, such as in a newspaper or Usenet post[2-5]. The timestamp proves that the data must have existed at the time, obviously, in order to get into the hash. Each timestamp includes the previous timestamp in its hash, forming a chain, with each additional timestamp reinforcing the ones before it.
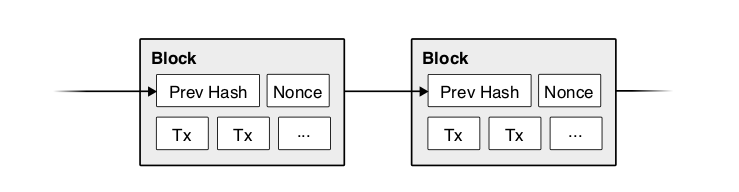
4. Proof-of-Work
To implement a distributed timestamp server on a peer-to-peer basis, we will need to use a proof-of-work system similar to Adam Back’s Hashcash[6], rather than newspaper or Usenet posts. The proof-of-work involves scanning for a value that when hashed, such as with SCRYPT, the hash begins with a number of zero bits. The average work required is exponential in the number of zero bits required and can be verified by executing a single hash.
For our timestamp network, we implement the proof-of-work by incrementing a nonce in the block until a value is found that gives the block’s hash the required zero bits. Once the CPU effort has been expended to make it satisfy the proof-of-work, the block cannot be changed without redoing the work. As later blocks are chained after it, the work to change the block would include redoing all the blocks after it.
The proof-of-work also solves the problem of determining representation in majority decision making. If the majority were based on one-IP-address-one-vote, it could be subverted by anyone able to allocate many IPs. Proof-of-work is essentially one-CPU-one-vote. The majority decision is represented by the longest chain, which has the greatest proof-of-work effort invested in it. If a majority of CPU power is controlled by honest nodes, the honest chain will grow the fastest and outpace any competing chains. To modify a past block, an attacker would have to redo the proof-of-work of the block and all blocks after it and then catch up with and surpass the work of the honest nodes. We will show later that the probability of a slower attacker catching up diminishes exponentially as subsequent blocks are added.
To compensate for increasing hardware speed and varying interest in running nodes over time, the proof-of-work difficulty is determined by a moving average targeting an average number of blocks per hour. If they’re generated too fast, the difficulty increases.
5. Network
The steps to run the network are as follows:
- New transactions are broadcast to all nodes.
- Each node collects new transactions into a block.
- Each node works on finding a difficult proof-of-work for its block.
- When a node finds a proof-of-work, it broadcasts the block to all nodes.
- Nodes accept the block only if all transactions in it are valid and not already spent.
- Nodes express their acceptance of the block by working on creating the next block in the chain, using the hash of the accepted block as the previous hash.
Nodes always consider the longest chain to be the correct one and will keep working on extending it. If two nodes broadcast different versions of the next block simultaneously, some nodes may receive one or the other first. In that case, they work on the first one they received, but save the other branch in case it becomes longer. The tie will be broken when the next proof-of-work is found and one branch becomes longer; the nodes that were working on the other branch will then switch to the longer one.
New transaction broadcasts do not necessarily need to reach all nodes. As long as they reach many nodes, they will get into a block before long. Block broadcasts are also tolerant of dropped messages. If a node does not receive a block, it will request it when it receives the next block and realizes it missed one.
6. Incentive
By convention, the first transaction in a block is a special transaction that starts a new coin owned by the creator of the block. This adds an incentive for nodes to support the network, and provides a way to initially distribute coins into circulation, since there is no central authority to issue them. The steady addition of a constant of amount of new coins is analogous to gold miners expending resources to add gold to circulation. In our case, it is CPU time and electricity that is expended.
The incentive can also be funded with transaction fees. If the output value of a transaction is less than its input value, the difference is a transaction fee that is added to the incentive value of the block containing the transaction. Once a predetermined number of coins have entered circulation, the incentive can transition entirely to transaction fees and be completely inflation free.
The incentive may help encourage nodes to stay honest. If a greedy attacker is able to assemble more CPU power than all the honest nodes, he would have to choose between using it to defraud people by stealing back his payments, or using it to generate new coins. He ought to find it more profitable to play by the rules, such rules that favour him with more new coins than everyone else combined, than to undermine the system and the validity of his own wealth.
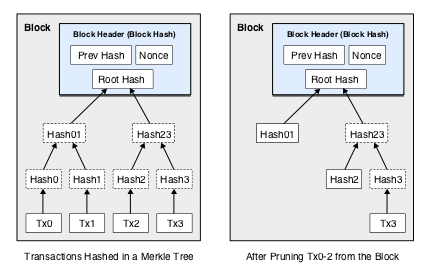
7. Reclaiming Disk Space
Once the latest transaction in a coin is buried under enough blocks, the spent transactions before it can be discarded to save disk space. To facilitate this without breaking the block’s hash, transactions are hashed in a Merkle Tree [7][2][5], with only the root included in the block’s hash. Old blocks can then be compacted by stubbing off branches of the tree. The interior hashes do not need to be stored.
A block header with no transactions would be about 80 bytes. If we suppose blocks are generated every 2.5 minutes, according to Moore’s Law storage should not be a problem even if the block headers must be kept in memory.
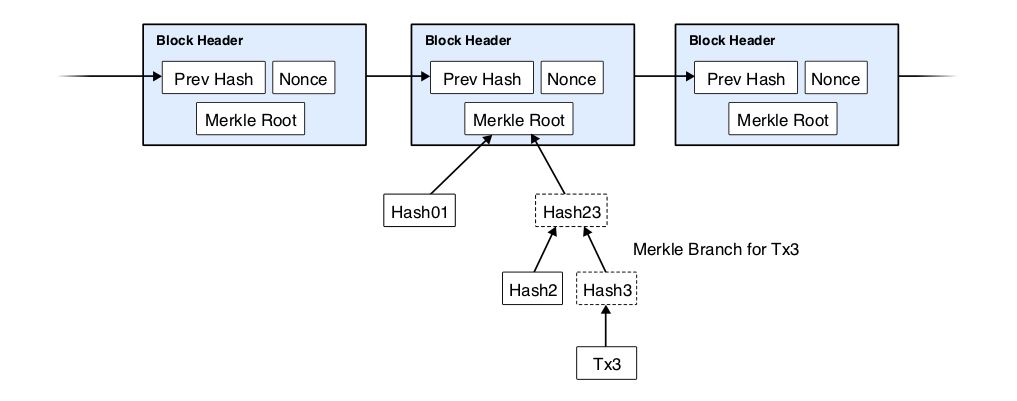
8. Simplified Payment Verification
It is possible to verify payments without running a full network node. A user only needs to keep a copy of the block headers of the longest proof-of-work chain, which he can get by querying network nodes until he’s convinced he has the longest chain, and obtain the Merkle branch linking the transaction to the block it’s timestamped in. He can’t check the transaction for himself, but by linking it to a place in the chain, he can see that a network node has accepted it, and blocks added after it further confirm the network has accepted it.
As such, the verification is reliable as long as honest nodes control the network, but is more vulnerable if the network is overpowered by an attacker. While network nodes can verify transactions for themselves, the simplified method can be fooled by an attacker’s fabricated transactions for as long as the attacker can continue to overpower the network. One strategy to protect against this would be to accept alerts from network nodes when they detect an invalid block, prompting the user’s software to download the full block and alerted transactions to confirm the inconsistency. Businesses that receive frequent payments will probably still want to run their own nodes for more independent security and quicker verification.
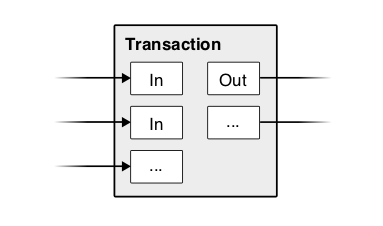
9. Combining and Splitting Value
Although it would be possible to handle coins individually, it would be unwieldy to make a separate transaction for every cent in a transfer. To allow value to be split and combined, transactions contain multiple inputs and outputs. Normally there will be either a single input from a larger previous transaction or multiple inputs combining smaller amounts, and at most two outputs: one for the payment, and one returning the change, if any, back to the sender.
It should be noted that fan-out, where a transaction depends on several transactions, and those transactions depend on many more, is not a problem here. There is never the need to extract a complete standalone copy of a transaction’s history.
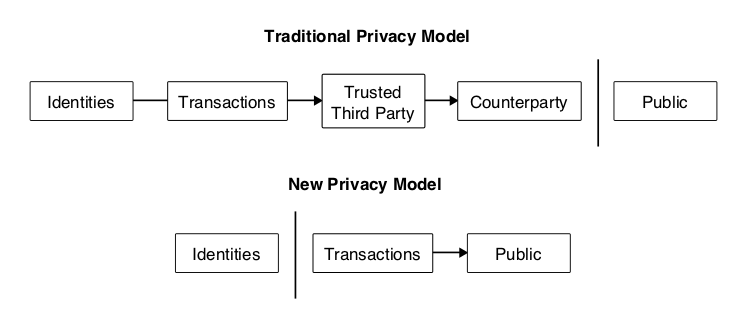
10. Privacy
The traditional banking model achieves a level of privacy by limiting access to information to the parties involved and the intermediary third party. The necessity to announce all transactions publicly precludes this method, but privacy can still be maintained by breaking the flow of information in another place: by keeping public keys anonymous. The public can see that someone is sending an amount to someone else, but without information linking the transaction to anyone. This is similar to the level of information released by stock exchanges, where the time and size of individual trades, the “tape”, is made public, but without telling who the parties were.
As an additional firewall, a new key pair should be used for each transaction to keep them from being linked to a common owner. Some linking is still unavoidable with multi-input transactions, which necessarily reveal that their inputs were owned by the same owner. The risk is that if the owner of a key is revealed, linking could reveal other transactions that belonged to the same owner.
11. Calculations
We consider the scenario of an attacker trying to generate an alternate chain faster than the honest chain. Even if this is accomplished, it does not throw the system open to arbitrary changes, such as creating value out of thin air or taking money that never belonged to the attacker. Nodes are not going to accept an invalid transaction as payment, and honest nodes will never accept a block containing them. An attacker can only try to change one of his own transactions to take back money he recently spent.
The race between the honest chain and an attacker chain can be characterized as a Binomial Random Walk. The success event is the honest chain being extended by one block, increasing its lead by +1, and the failure event is the attacker’s chain being extended by one block, reducing the gap by -1.
The probability of an attacker catching up from a given deficit is analogous to a Gambler’s Ruin problem. Suppose a gambler with unlimited credit starts at a deficit and plays potentially an infinite number of trials to try to reach breakeven. We can calculate the probability he ever reaches breakeven, or that an attacker ever catches up with the honest chain, as follows[8]:
Calculations
Given our assumption that p>q, the probability drops exponentially as the number of blocks the attacker has to catch up with increases. With the odds against him, if he doesn’t make a lucky lunge forward early on, his chances become vanishingly small as he falls further behind.
We now consider how long the recipient of a new transaction needs to wait before being sufficiently certain the sender can’t change the transaction. We assume the sender is an attacker who wants to make the recipient believe he paid him for a while, then switch it to pay back to himself after some time has passed. The receiver will be alerted when that happens, but the sender hopes it will be too late.
The receiver generates a new key pair and gives the public key to the sender shortly before signing. This prevents the sender from preparing a chain of blocks ahead of time by working on it continuously until he is lucky enough to get far enough ahead, then executing the transaction at that moment. Once the transaction is sent, the dishonest sender starts working in secret on a parallel chain containing an alternate version of his transaction.
The recipient waits until the transaction has been added to a block and z blocks have been linked after it. He doesn’t know the exact amount of progress the attacker has made, but assuming the honest blocks took the average expected time per block, the attacker’s potential progress will be a Poisson distribution with expected value:
λ=zqp
To get the probability the attacker could still catch up now, we multiply the Poisson density for each amount of progress he could have made by the probability he could catch up from that point:
∑k=0∞λke−λk!⋅{(q/p)(z−k)1ifk≤zifk>z}
Rearranging to avoid summing the infinite tail of the distribution…1−∑k=0zλke−λk!(1−(q/p)(z−k))
Converting to C code…#include
double AttackerSuccessProbability(double q, int z)
{
double p = 1.0 – q;
double lambda = z * (q / p);
double sum = 1.0;
int i, k;
for (k = 0; k <= z; k++)
{
double poisson = exp(-lambda);
for (i = 1; i <= k; i++)
poisson *= lambda / i;
sum -= poisson * (1 – pow(q / p, z – k));
}
return sum;
}
Running some results, we can see the probability drop off exponentially with z.q=0.1
z=0 P=1.0000000
z=1 P=0.2045873
z=2 P=0.0509779
z=3 P=0.0131722
z=4 P=0.0034552
z=5 P=0.0009137
z=6 P=0.0002428
z=7 P=0.0000647
z=8 P=0.0000173
z=9 P=0.0000046
z=10 P=0.0000012q=0.3
z=0 P=1.0000000
z=5 P=0.1773523
z=10 P=0.0416605
z=15 P=0.0101008
z=20 P=0.0024804
z=25 P=0.0006132
z=30 P=0.0001522
z=35 P=0.0000379
z=40 P=0.0000095
z=45 P=0.0000024
z=50 P=0.0000006
Solving for P less than 0.1%…P < 0.001
q=0.10 z=5
q=0.15 z=8
q=0.20 z=11
q=0.25 z=15
q=0.30 z=24
q=0.35 z=41
q=0.40 z=89
q=0.45 z=34012. Conclusion
We have proposed a system for electronic transactions without relying on intermediaries. We started with the usual framework of coins made from digital signatures, which provides strong control of ownership, but is incomplete without a way to prevent double-spending. To solve this, we proposed a peer-to-peer network using proof-of-work to record a public history of transactions that quickly becomes computationally impractical for an attacker to change if honest nodes control a majority of CPU power. The network is robust in its unstructured simplicity. Nodes work all at once with little coordination. They do not need to be identified, since messages are not routed to any particular place and only need to be delivered on a best effort basis. Nodes can leave and rejoin the network at will, accepting the proof-of-work chain as proof of what happened while they were gone. They vote with their CPU power, expressing their acceptance of valid blocks by working on extending them and rejecting invalid blocks by refusing to work on them. Any needed rules and incentives can be enforced with this consensus mechanism.
Sound Digital Money
$100 trillion dollar market. Payment Coin owes much of its strength and utility to its independence of authority and censorship resistance. Payment Coin as a currency is impossible to debase without the express consent of a majority of the network. A system, not relying on any level of trust whatsoever and whose only assumption is that every participant on average acts in their own perceived self-interest: the very foundation on which modern economic theory already rests.
Payments is one of the more obvious applications for borderless, permissionless value transfer protocols. Money can be transmitted anywhere in the world where there is access to electricity and the Internet, with flat fees regardless of amount transferred. A Payment Coin transaction will cost the same whether you are sending POD 0.001 or POD 100,000.
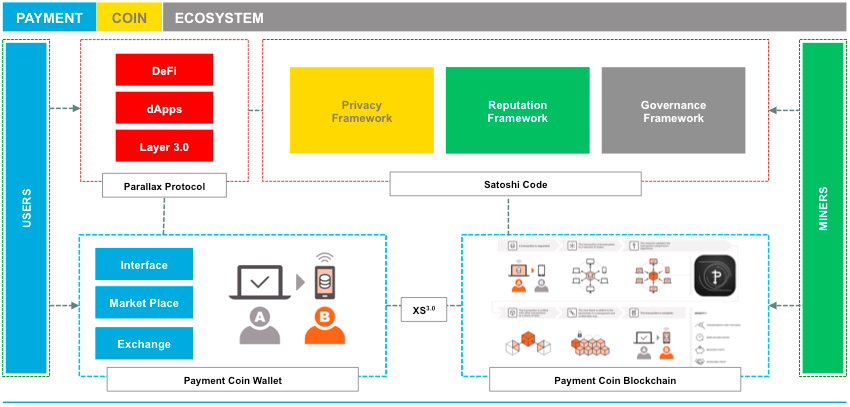
Payment Coin Ecosystem (Beyond the Whitepaper)
Since the first altcoins began emerging a few years after Bitcoin’s invention there has been an explosion of new coins and tokens in the cryptocurrency space. Altcoins now number in the thousands, and with the rapid proliferation of ERC-20 tokens, this trend has only accelerated.
However there has been only a dozen true breakthroughs since Bitcoin. However none have been able to complete the blueprint that Satoshi Nakamoto laid out between 2008-2010.
2009 –> Bitcoin –> 2011 –> Litecoin –> 2012 –> Cryptonote –> 2014 –> Monero –> 2016 –> Zcash –> 2017 –> Bitcoin Cash –> 2018-22 –> Payment Coin
Payment Coin R&D Context
Ever since the music sharing website, Napster, was introduced in June 1999, peer-to-peer system usage has dominated the Internet traffic together with the Web, Decentralized architecture has become a viable alternative to the traditional client-server based models in the realm of large scale distributed systems. Our coin symbol POD was selected as it represents the Power of Decentralization (POD). Our roadmap is fluid and continuously evolves and innovates:
- Decentralization: Wallet embedded Marketplace, Trust-based incentive mechanism, Trade-based incentive mechanism.
- Privacy and Trust: Enhanced psuedo-anonynomity, or private balances to overcome Bitcoin transactions public nature and increasing requirements for user privacy.
- Concept Wallet: Mobile money extension for 2 billion + unbanked. Developing countries without traditional tier one infrastructures.
Modern cryptocurrencies are suffering the same challenges faced by PGP and other crypto related products over the last two decades. Mass adoption usability and utility. The team at Payment Coin understand the complexities and have all the ingredients for resolution. By learning from the past via our world beating research, we are building the best cryptocurrency for the future.